How the Address Poisoning Scam Targets Your Crypto Wallet
How often do you check crypto addresses before sending and receiving coins? How many times do you use the same address for the same operations? Just think about it—scammers do it every day.
According to Chainalysis research, crypto address scams have been steadily becoming the most popular type of scam since 2024. Unfortunately, the situation in 2026 is no better. According to Scam Sniffer, roughly $6.27 million was stolen from 4,741 victims in January 2026, a 207% increase compared to December 2025.
Let's look at this type of scam in detail and discuss how not to become a victim.
What Is an Address Poisoning Scam?
Let's imagine that you regularly send some coins to the same address. It does not matter whether it is your second personal address in another wallet or another person’s address. You are used to sending crypto automatically, and you usually just copy the address from the History section.
Meanwhile, scammers explore blockchain transaction patterns every day and try to find matches between addresses. If you send coins to the same address all the time, scammers will notice that, and you will become a target.
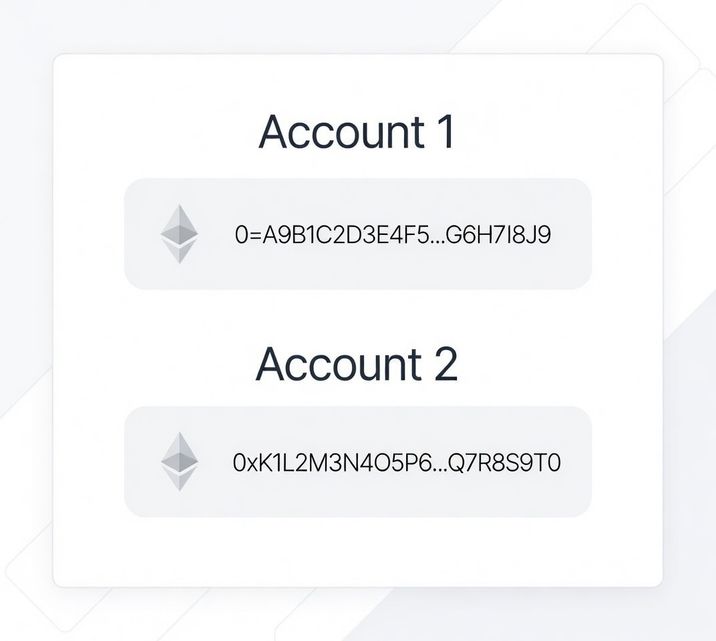
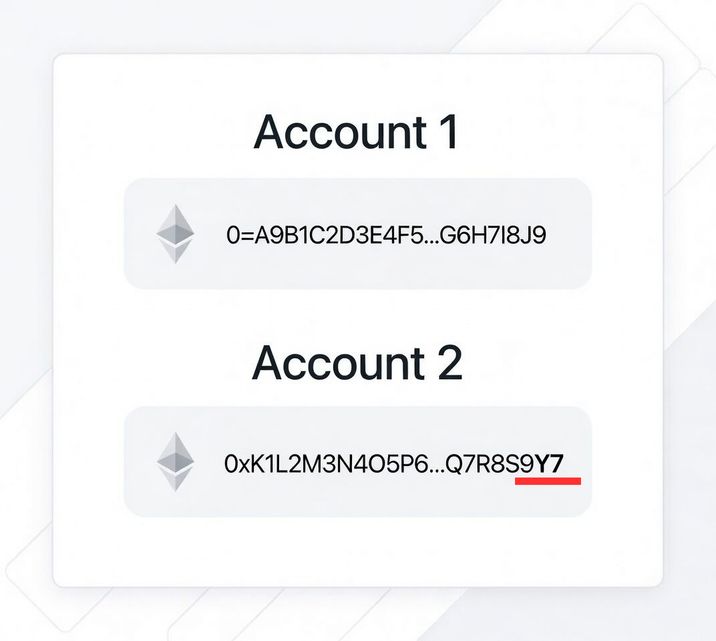
- Scammers create a lookalike address that the victim most often interacts with. The difference can be in a few symbols, which you may not recognize at first glance.
- Then, they send a small, seemingly harmless transaction (it is called a dust transaction) from this newly generated address, effectively “poisoning” the target’s address book.
- The scammers then wait for you to make a mistake and send money to the new scam address. If that happens, your crypto will be stolen.
Thus, an address poisoning scam is a type of cyber fraud in which you send coins to a fake crypto address that “poisons” your address book by mimicking a real one.
How Do Scammers Create a Lookalike Address?
Of course, scammers do not pick existing addresses but instead generate new ones en masse with a specified prefix or suffix so that they visually resemble the victim's address. As a rule, generating absolutely identical addresses is impossible, so attackers try matching the first or last 2–6 symbols.
There are many services that can create a new fake address. For example, Vanitygen and VanitySearch are used for BTC, while Profanity and Vanity-ETH are used for ETH. However, these utilities are public and scammers prefer to use custom tools. They are often based on GPU farming or open-source solutions.
How Can You Protect Yourself?
The core of address poisoning scam is exploitation of your inattentiveness.
1. Never Copy an Address From Transaction History
This is the most common mistake. Scammers deliberately create “vanity” addresses so that when you scroll through your wallet history, both addresses look nearly identical at a glance.
Always copy the recipient address directly from the original trusted source (official website, verified contact, hardware wallet screen).
Never reuse an address from your transaction log without verifying it fully. In addition, add important addresses to your address book.
2. Verify the Entire Address — Not Just the First and Last Characters
Most users check only the first 4 and last 4 symbols. That’s no longer enough. Attackers generate addresses that intentionally match those positions.
Best practice:
- Verify at least the first 6 and last 6 characters.
- For large transfers, compare the full address side-by-side.
- If possible, paste the address into a text editor and manually scan it before confirming.
If you’re sending five or six figures, spending 10 extra seconds verifying the full string is not optional—it’s mandatory.
3. Send a Small Test Transaction First
Instead of sending the full balance at once, start with a small amount and confirm that it reaches the intended recipient. Then verify the address on-chain and ensure everything matches exactly before moving the remaining funds.
Yes, this approach costs an additional network fee. But compared to the irreversible loss of a large transfer, that fee is negligible. Address poisoning scams rely on haste and overconfidence. A two-step transaction process forces you to slow down and dramatically reduces the risk of sending funds to a lookalike address.
4. Use Hardware Wallet Confirmation Screens
If you use a hardware wallet, the device screen should be treated as the ultimate verification point. Malware can alter clipboard data, replace copied addresses, or manipulate what appears in your browser. What it cannot change is the address displayed on your hardware device itself.
Before confirming any transaction, carefully compare the recipient address shown on the hardware wallet screen with the intended address from your trusted source. Check the network and the amount as well. Never approve a transaction without verifying these details directly on the device. That extra step is not optional—it’s the primary defense against address manipulation.
5. Separate Wallets and Limit Address Reuse
To reduce this risk, separate your funds by purpose. Use one wallet for long-term storage and another for daily transactions. Avoid publicly exposing your primary holdings address. When possible, generate fresh receiving addresses instead of relying on the same one repeatedly. Operational separation makes it harder for attackers to predict your behavior and target you effectively.
6. Double-Check Addresses on Blockchain Explorers
Before executing a high-value transfer, take an extra minute to verify the recipient address using a blockchain explorer. Review its transaction history and behavioral pattern. Poisoning addresses often show repetitive dust transfers to multiple unrelated wallets—a clear indicator of automated scam activity.
Read more: Why Crypto Exchanges and Blockchain Explorers Show Different Balances
If the address appears newly created, unusually inactive, or primarily associated with small outbound transfers to random wallets, pause the transaction and re-verify the source. A quick on-chain review can expose suspicious patterns that are not immediately visible in your wallet interface.